Tech
The Vibecoding Disaster: 04 Surprising Truths from the Mercor AI Data Breach


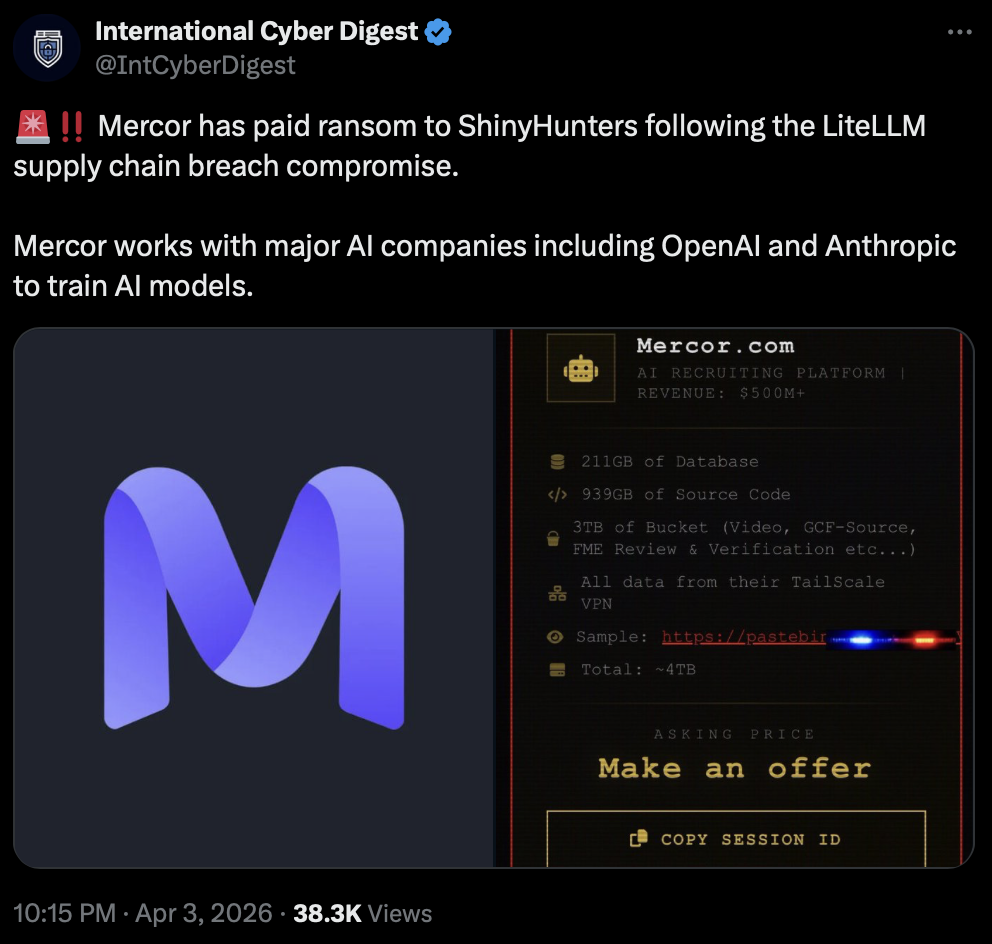
TL;DR
The 40-Minute Meltdown We have entered an era where we outsource our professional identities to black boxes and call it progress. We trust our AI gateways and security tools impli…
The 40-Minute Meltdown
We have entered an era where we outsource our professional identities to black boxes and call it progress. We trust our AI gateways and security tools implicitly, treating them as bulletproof shields.
The Mercor AI breach provides a sobering autopsy of how fragile that trust truly is.
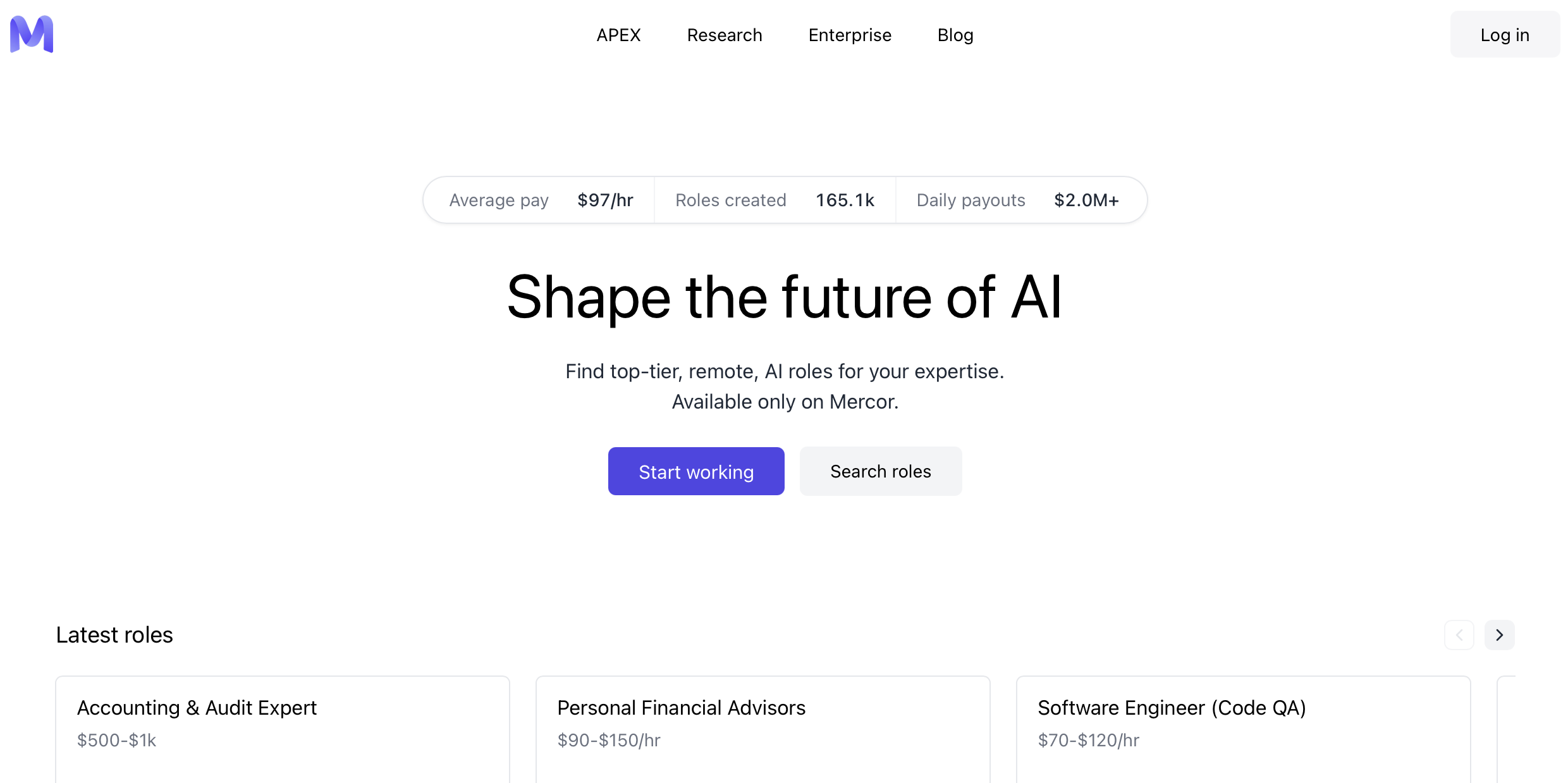
Mercor AI, a platform valued in the billions and designed to connect experts to titans like OpenAI and Anthropic was crippled in less than an hour. A supply chain attack that lasted a mere 40 minutes managed to compromise a company facilitating over $2 million in daily payouts.
This was a high-speed wreck in the heart of the AI gold rush. We assumed the gatekeepers were secure because they were expensive. But boy we were wrong...
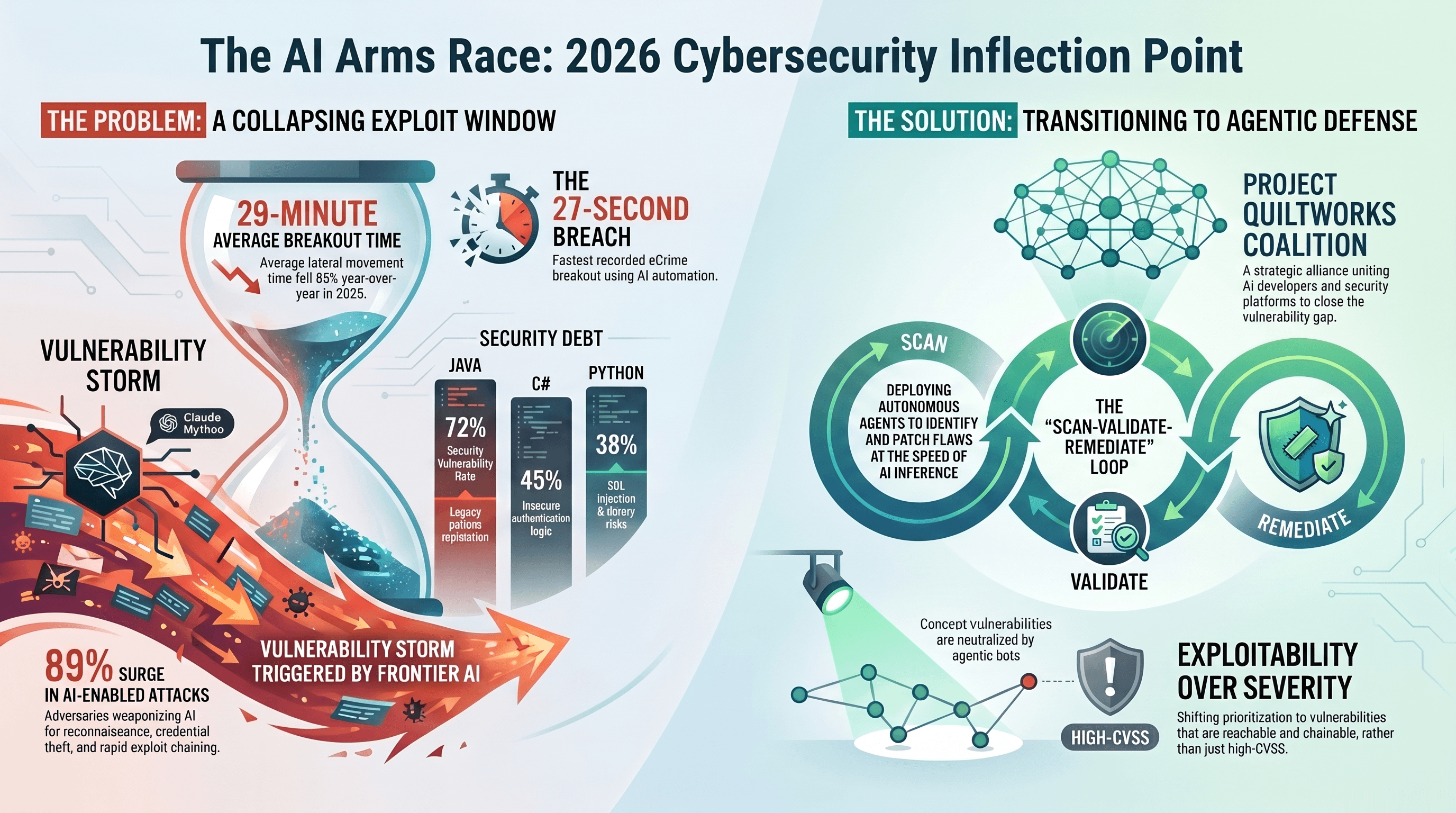
The 40-Minute Domino Effect
The breach was not a direct frontal assault on Mercor’s fortress but a case of "upstreaming the poison."
According to Unit 42, the threat group TeamPCP compromised the PyPI publishing credentials for the LiteLLM library. LiteLLM isn't some obscure script; it boasts over 95 million monthly downloads and serves as a critical routing gateway for AI applications.
Malicious versions (1.82.7 and 1.82.8) were live for only 40 minutes, yet the scale was staggering. Wiz estimates that this brief window potentially impacted 500,000 machines across 36% of all cloud environments. In modern cyberwarfare, data exfiltration happens in under 60 seconds once the malware executes.
The attack effectively turned the tools meant to protect infrastructure into the vehicles for its destruction. By the time a human could even blink at a dashboard, the keys to the kingdom were already gone.
"Unlike past supply chain attacks, this operation explicitly weaponizes security and developer infrastructure that inherently require elevated privileges. This allows attackers unimpeded access to production secrets." — Unit 42 Report
Why Compliant Doesn't Mean "Secure"
In the fallout, a heated debate ignited on Hacker News regarding Mercor’s security "pedigree."
The company had undergone verification by a legitimate audit firm yet this failed to prevent a total exfiltration of 4 TB of data. This underscores what skeptics call the "liability transfer framework", the idea that SOC2 and ISO27001 are often just forms of compliance cosplay used to lower insurance premiums.

Audits are about checking boxes but security is about stopping bullets. The theft of 4TB comprising 939GB of source code, 211GB of databases, and 3TB of storage buckets proves that a certificate on the wall is not a firewall.
Compliance: A standardized method for communicating activity to outside parties to satisfy insurance and contract requirements.
Capability: The technical rigor required to defend against 0-day supply chain attacks and maintain actual infrastructure integrity.
The Privacy Nightmare
The breach was a wholesale theft of human identity.
Of the 4TB stolen, 3TB consisted of storage buckets containing highly sensitive "Know Your Customer" (KYC) data. This included video interviews and passport scans belonging to thousands of job seekers who believed their privacy was a foundational priority.
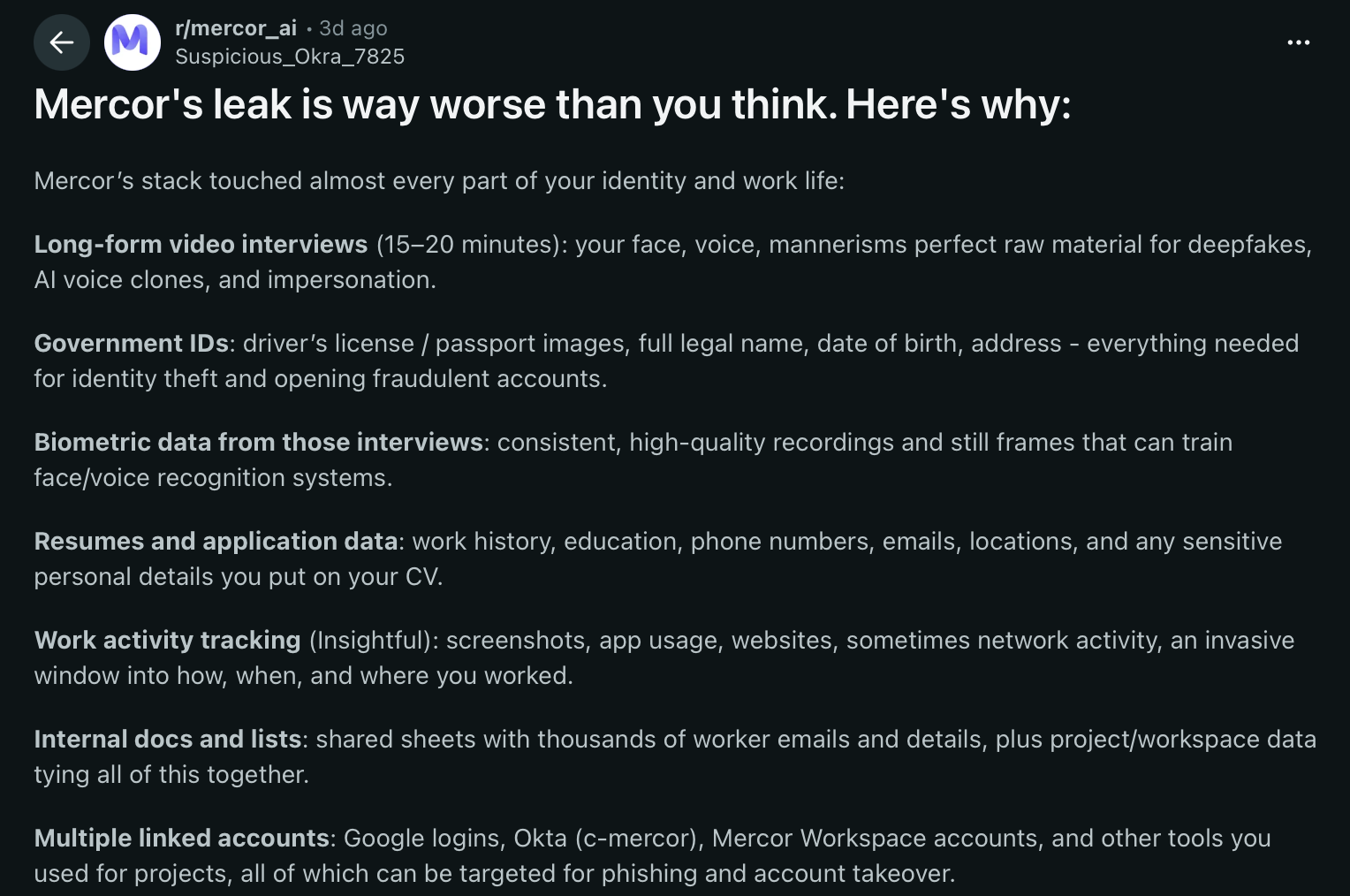
The most disturbing, if not unverified, glimpse into the company culture came from reports on social media. Internal screenshots allegedly leaked from the breach showed user interviews renamed with vulgar and unprofessional titles. It suggests an internal culture where the people being "AI-vetted" were viewed as data points or punchlines rather than human beings.
Furthermore, the presence of insightful monitoring software in the data haul raises systemic privacy alarms. These tools capture IP addresses, browser activity and sensitive personal metadata.
For a job seeker, the convenience of an AI platform now looks more like an invasive surveillance dragnet.
The Rise of "Vibecoding"
A recurring theme in this post-mortem is vibecoding.
Popularized in developer circles, the term describes a culture of rapid, AI-assisted development that prioritizes "vibe" and shipping speed over rigorous infrastructure. In a vibecoding environment, basic security hygiene is treated as a secondary concern.
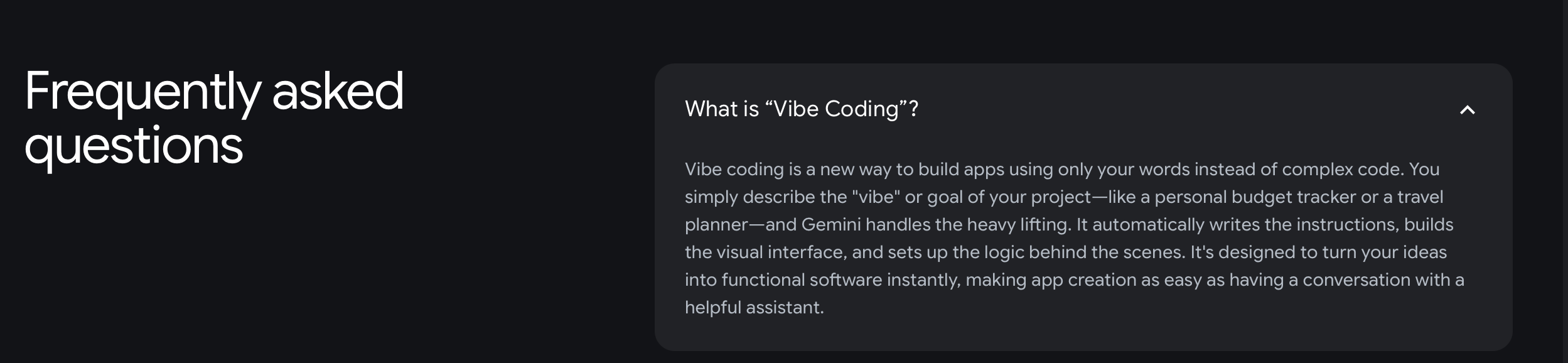
The technical evidence of this mindset was a catastrophic lack of isolation between development and production environments. When developers "move fast and break things," they often forget that the "things" being broken are the digital lives of their users. This governance failure provided a direct path for extortionists.
The consequences of this "vibe-first" approach are now being settled in dark web auctions. The Lapsus$ hacking group is reportedly auctioning the Mercor cache to the highest bidder. When a startup's growth outpaces its governance, it stops being a tech success story and starts being a high-value target for global extortion syndicates.
The New Era of Radical Transparency
The Mercor AI disaster serves as a definitive warning: a company’s security is only as strong as its least-known open-source dependency. We are entering a period of radical transparency, where a single 40-minute window can expose the inner workings and private data of a multi-billion-dollar enterprise.
The compliant shields of the past are proving insufficient against sophisticated upstream compromises. As our professional lives move further into the cloud, the risk to our digital identities becomes permanent and non-negotiable.
In an era where your video interview can be deepfaked and your passport is for sale on the dark web, is the convenience of AI-driven recruitment worth the permanent risk to your digital identity?