Tech
Why Your Locked iPhone Might Be Less Secure Than You Think

TL;DR
A specialised hack reveals a massive loophole in the Apple Pay and Visa ecosystem, allowing thieves to drain thousands from a phone that never even leaves your pocket. Here’s how the ultimate digital pickpocketing works and why the companies involved haven’t fixed it since the hack went public it 2021...
Imagine a street magic trick with a terrifying financial twist. You place your locked iPhone face-down on a table. You never touch the screen, you never enter a passcode, and you certainly don't look at the FaceID sensors. Yet, a nearby payment terminal chimes, a receipt scrolls out, and $10,000 vanishes from your bank account.
This is a real loophole hidden in plain sight.
Veritasium recently pulled off this exact stunt on tech reviewer Marques Brownlee (MKBHD), proving that the device in your pocket might be authorising massive payments while you aren't even looking.
It’s an exploit that turns a feature meant for your everyday convenience into a digital vacuum for your savings.
Here is exactly how they pull it off.
The Commuter’s Achilles Heel
The vulnerability relies on a convenient loophole: not having to unlock your phone to ride the subway.
To make commuting seamless, Apple introduced Express Transit Mode in 2019. It allows you to tap your phone at a transit gate without the friction of FaceID or a passcode. You just tap, the gate opens, and you catch your train.
But that convenience is a Trojan Horse. Professors loana Boureanu and Tom Chothia from the University of Surrey discovered they could mimic the exact "open sesame" signal used by those transit gates.

Armed with laptops and a $300 scanning device called a Proxmark, they went to the London Underground and recorded exactly what the turnstiles were "saying" to commuters' iPhones.
When your phone hears this specific code, it lowers its guard. It assumes you’re just a commuter in a hurry and prepares to pay a few dollars without asking for your biometric permission.
The Lies We Tell Ourselves
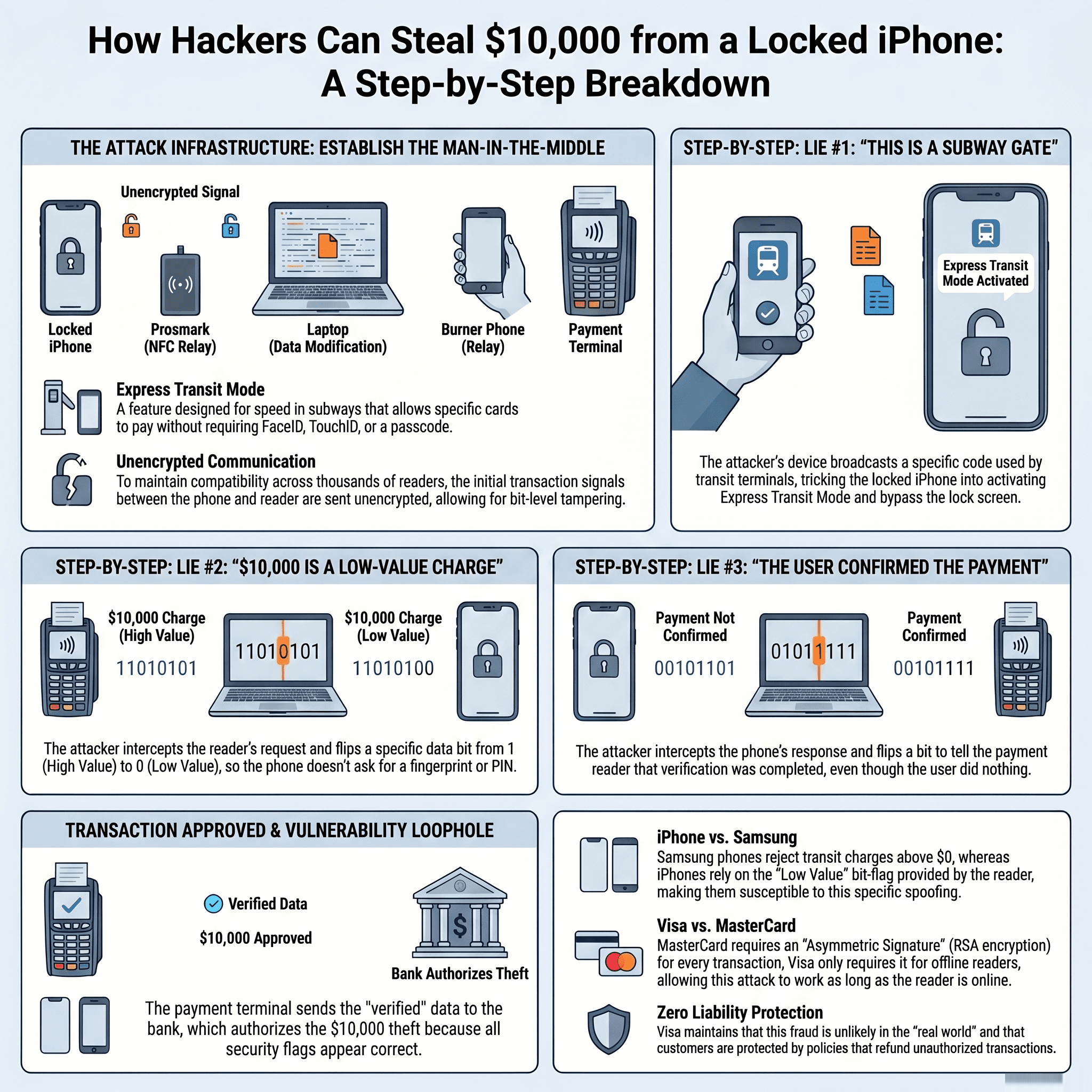
Once the phone’s guard is down, the hackers have to bypass the bank's spending limits. Normally, a massive purchase triggers an immediate demand for a PIN or FaceID. To avoid this, the attackers use a technique called "bit flipping."
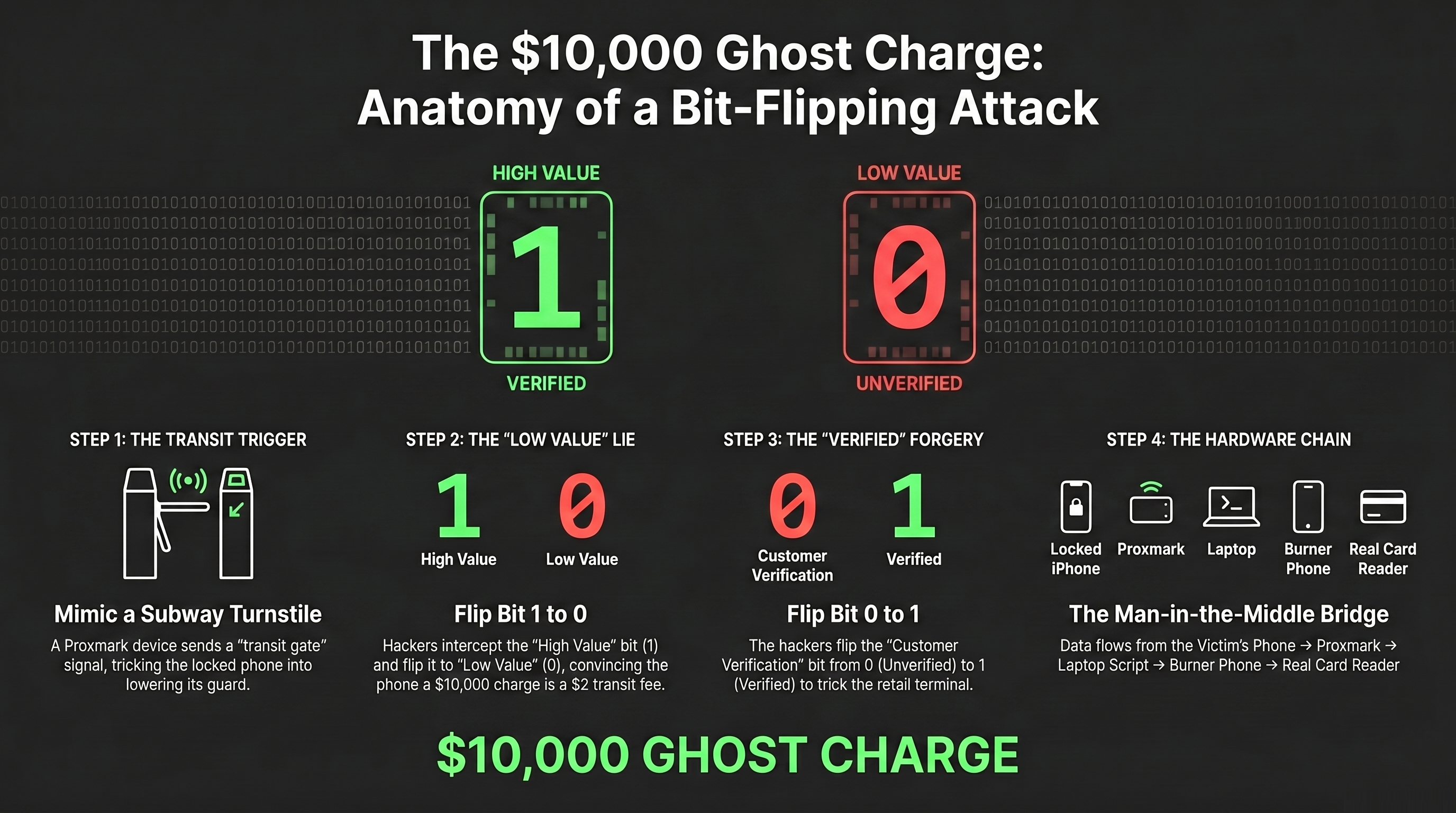
Your iPhone doesn't actually read the number "$10,000" to decide if a transaction is too large. Instead, it looks for a single bit of binary data in the message sent by the card reader. This flag exists so different countries can set their own "high value" limits without banks having to issue new cards.
Using a Python script, the hackers intercept the reader's signal and literally flip that digital flag from a 1 (High Value) to a 0 (Low Value). By altering that single digit, the hackers convince your phone that a $10,000 charge is just a cheap transit ticket.
The Final Lie
But the deception isn't over. Even if the phone is tricked, the actual retail payment terminal should reject the transaction.
Why?
Because the phone’s automated response technically tells the terminal: "I am paying $10,000, but the user hasn't verified this with a PIN or FaceID."
This triggers the third and final lie. Before the phone’s reply reaches the card reader, the hackers intercept it. They locate the "Customer Verification" bit and flip it from a 0 (unverified) to a 1 (verified).
Now, the card reader is happy. It receives a forged message stating that you successfully provided your fingerprint or FaceID. It passes this "proof" to the bank, and the money is gone.
The Anatomy of a Digital Heist
In the cybersecurity world, this is known as a Man-in-the-Middle (MITM) attack. The thieves act as an invisible bridge between your pocket and a real payment terminal using a chain of devices:
Your Locked Phone: Sitting quietly in your pocket or on a table.
The Proxmark: A device near you that tricks your phone into thinking it’s at a subway gate.
The Hacker's Laptop: The "brain" running the bit-flipping scripts in real-time.
A Burner Phone: Receives the modified, forged data and taps it against...
The Real Card Reader: The actual retail terminal where the $10,000 theft is finalized.
This works because the communication between the phone and the reader is sent unencrypted over the air. Anyone with the right tools can overhear, edit and pass along the conversation before either device realises what happened.
The Visa Blindspot
If you use a Samsung phone or a MasterCard, you can actually breathe a sigh of relief.
When a Samsung phone enters transit mode, it ignores the "low value" label entirely. It checks the actual price and only accepts charges of exactly $0 (allowing the transit provider to bill the user later).
MasterCard, on the other hand, uses complex asymmetric cryptography to mathematically "seal" the transaction data. If a hacker tries to flip even one bit of data to change the amount, the mathematical seal breaks. The reader sees the broken seal and kills the transaction.
Visa’s vulnerability, however, is a choice of architecture. While the iPhone does send a digital signature to Visa to prove the data is untampered, Visa’s system only requires the terminal to check that signature for "offline" transactions. Because the hackers ensure the payment terminal is online during the attack, the Visa system simply ignores the signature entirely.
The Price of Convenience
This vulnerability has been public knowledge since 2021, yet the loophole remains unpatched. Apple points the finger at Visa, while Visa points to its "Zero Liability Policy," assuring customers they will be refunded for fraud because such attacks are statistically "unlikely."
But statistics are cold comfort when your rent money is gone. We shouldn't view financial security as a game of odds. If airlines treated plane crashes as an "inevitable cost of business," we’d never fly. When a system touches millions of lives, forcing victims to notice the fraud, dispute it, and wait weeks for a refund is a failure of engineering, not a feature of security.
Until the giants at Apple and Visa decide to close this gap, the responsibility falls on you. Fortunately, you can protect yourself in seconds:
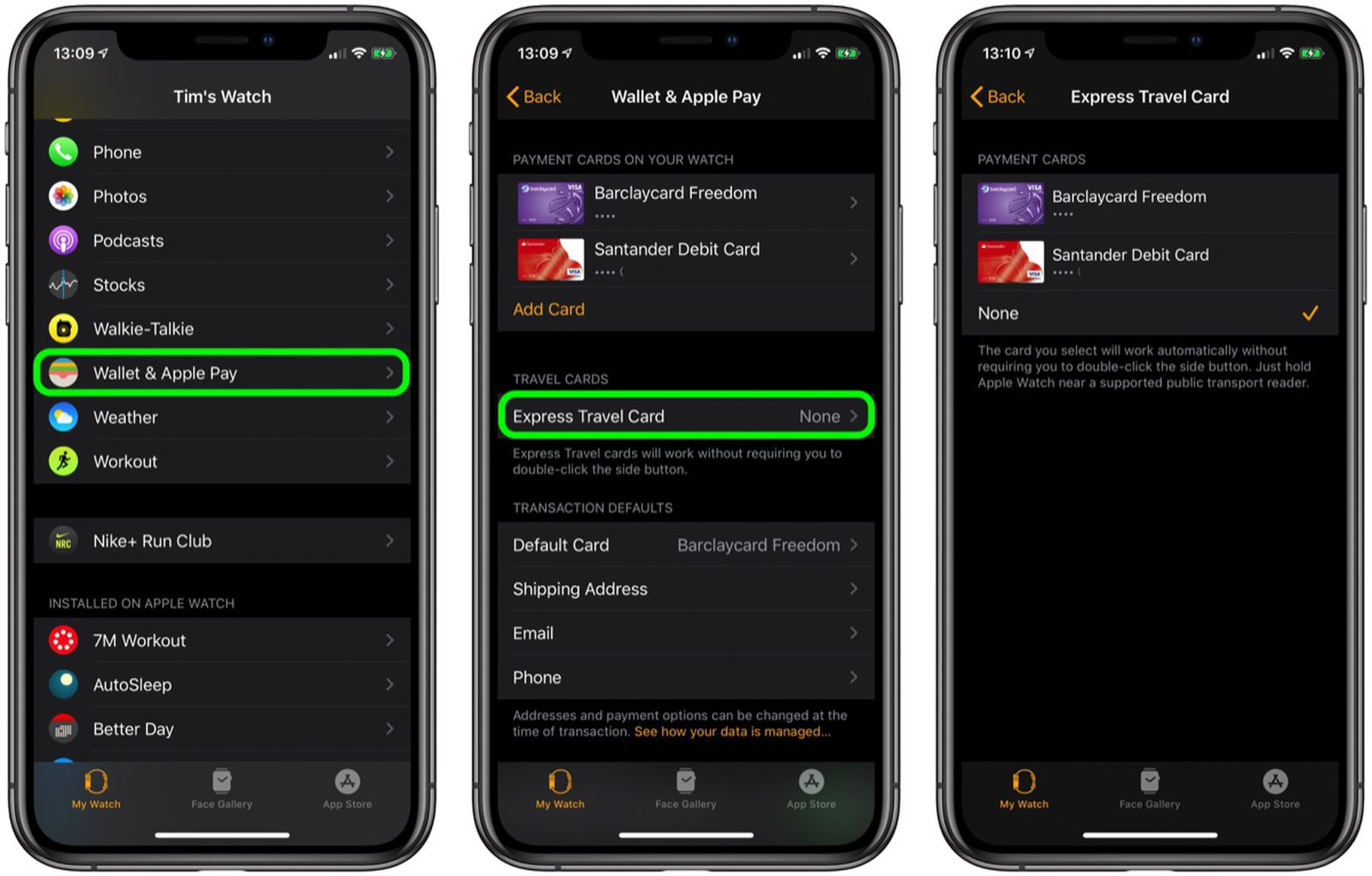
Disable Express Transit Mode: Go to your iPhone's Wallet & Apple Pay settings, tap Express Transit Card, and set it to None.
Switch Your Transit Card: If you absolutely need the tap-and-go feature, use a MasterCard or a non-Visa card for your transit slot.
We live in an age of frictionless convenience, but we shouldn't have to accept probable fraud as the price of a faster commute.
It’s time we demand that the companies holding our money prioritise our security over their convenience.